

Cyber Insurance Compliance Audit
Our platform enables you to receive a tailored AI-powered approach that suits your needs and helps you stay one step ahead.
.png)
Receive exact types of Cybersecurity Products
.png)
No need to overpay for extra services

Fast decision process

Free cybersecurity assessment of your organisation
Cybersecurity
.png)

Cybersecurity education and compliance examination, Penetration system testing with quarterly undercover phishing simulation engraves a cybersecurity culture within your organisation.
We act as partners to our customers, helping them improve their cyber risk posture by providing free cybersecurity assessments of your organisation.
BCG has developed a unique, tailored solution for SMEs and large corporate organisations

We have developed a unique two-stage AI-powered approach that helps you stay one step ahead. Integrating undercover phishing testing with a detailed report creates a tailored cyber education approach.
AI-Powered Security Assessment

By carrying out security exercises where a cyber-security expert attempts to find and exploit vulnerabilities in a computer system. The purpose of this simulated attack is to identify any weak spots in a system's defences that attackers could take advantage of.
Penetration System Testing

After completing our interactive education course, your employee will receive certification that generally will improve the cybersecurity strength of your organisation. BCG Integrates quarterly undercover phishing simulation tests and cybersecurity training to reduce cyber risks and build a security culture within your organisation.
Education and compliance examination

BCG has developed a unique, tailored solution for SMEs and large corporate organisations. We act as partners to our customers, helping them improve their cyber risk posture by providing free cybersecurity assessments of your organisation. Cybersecurity education and compliance examination, Penetration system testing with quarterly undercover phishing simulation engraves a cybersecurity culture within your organisation.
Cyber Insurance Compliance Audit
The services we provide

Education and examination
We have developed a unique two-step approach based on artificial intelligence
AI-POWERED
PHISHING TEST
.png)
.png)
RESULTS REPORTS
.png)
EDUCATION AND
EXAMINATION
.png)
QUARTERLY
UNDERCOVER TESTS
.png)
RESULTS REPORTS

BEFOR
.png)
Identification of vulnerabilities in a computer system.
The purpose of this simulated attack is to identify any weak spots in a system’s defences that attackers could take advantage of.
.png)
AFTER

After completing a pen test, the organisation receive a detailed cyber report.
Based on the cyber report, you can implement security upgrades to plug up any vulnerabilities found during the test.
VS
Penetration System Testing
Blog
Latest blog
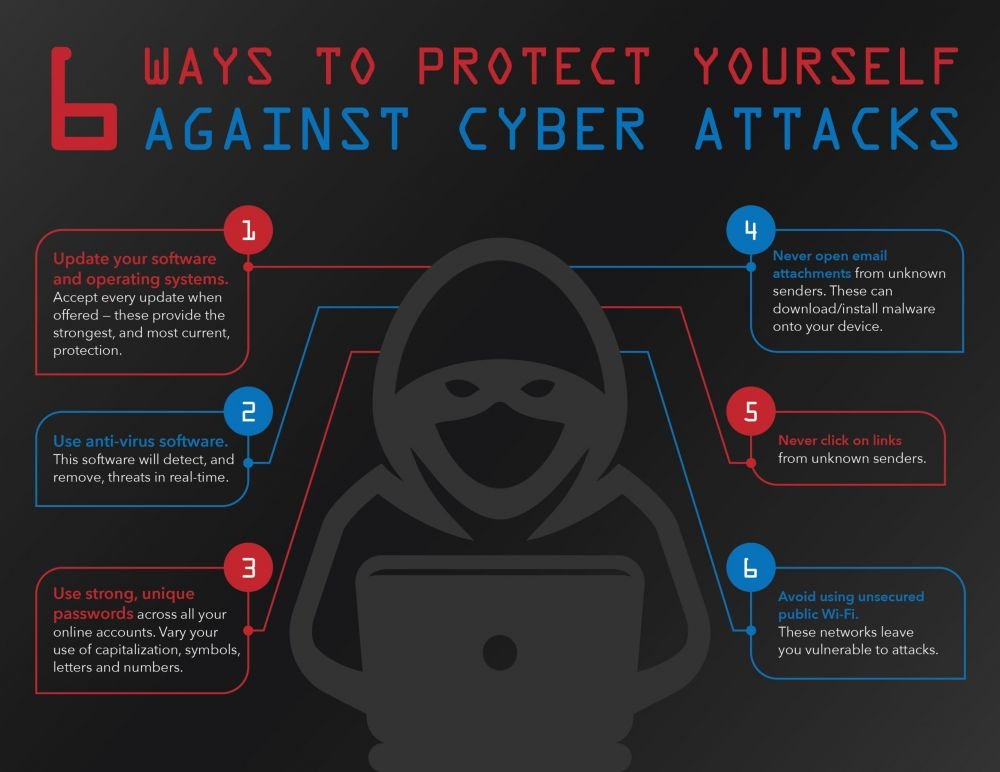
Protection against Cyber Attacks: Guaranteeing Security in the Internet World
What to do if your business is subject to a cyber attack? find out about main steps that will help to you fast to react on threats and minimize damage . Our recommendations will help to you stay ahead cybercriminals .
24 May 2024
Powered by Industry-Leading Technology






How cybercrime may affect your organisation

leakage of sensitive information
Organisation secrets can be stolen
.png)
Financial losses
Money can be stolen, converted into cryptocurrencies and passed through a mixer to mask further trace
.png)
Operational disruption
Corporate data can be encrypted or destroyed. This can lead to a freeze in all your organisation's operational activities
.png)
Lost revenue
Impact the relationship between the company
and its customers
.png)
Reputational damage
Customers, and even suppliers, may feel less secure leaving their sensitive information in the hands of a company whose IT infrastructure was broken at least once before
.png)
Legal consequences
Non-compliance with data protection regulations and laws can result in legal actions, fines, and penalties, increasing financial burden and further damaging the organization’s reputation




